Git is cryptographically secure, but it’s not foolproof. If you’re taking work from others on the internet and want to verify that commits are actually from a trusted source, Git has a few ways to sign and verify work using GPG.
Introduction to GPG
First of all, if you want to sign anything you need to get GPG configured and your personal key installed.
hzxie@XieHaozhe-PC:~$ gpg --list-keys
/home/hzxie/.gnupg/pubring.gpg
------------------------------
pub 1024D/381BA480 2007-02-15
uid Johannes Ranke (CRAN Debian archive) <jranke@uni-bremen.de>
pub 4096R/3DBF9592 2016-03-28
uid Haozhe Xie (GPG key for GitHub) <cshzxie@gmail.com>
sub 4096R/BFEB9969 2016-03-28
If you don’t have a key installed, you can generate one with gpg --gen-key.
gpg --gen-key
Once you have a private key to sign with, you can configure Git to use it for signing things by setting the user.signingkey config setting.
# Remember to replace the key here
git config --global user.signingkey 3DBF9592
git config --global commit.gpgsign true
Now Git will use your key by default to sign tags and commits if you want.
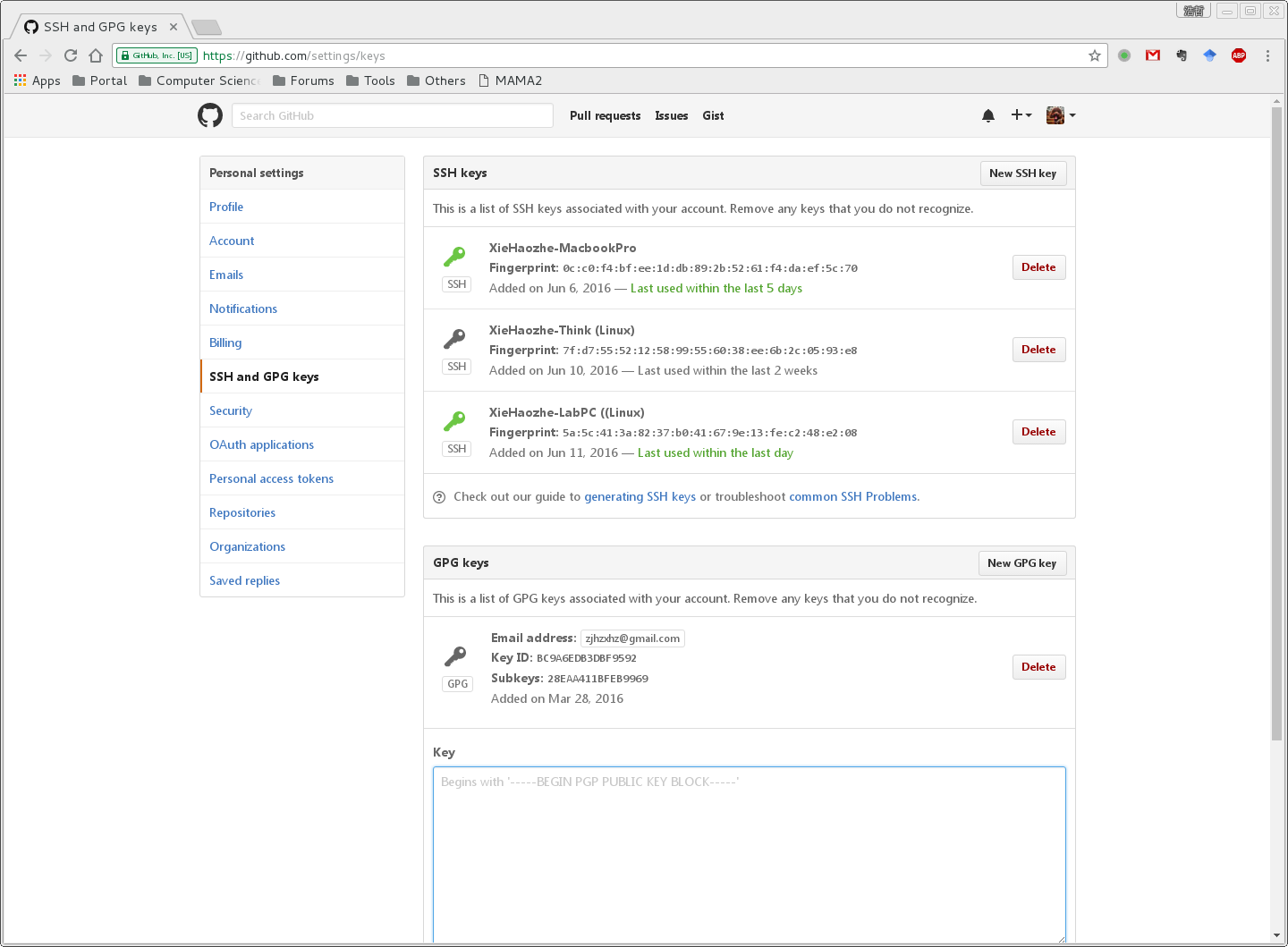
Add GPG Keys to GitHub
From the list of GPG keys, copy the GPG key ID you’d like to use. In this example, the GPG key ID is 3DBF9592. Then run following commands:
gpg --armor --export 3DBF9592
Copy your GPG key, beginning with -----BEGIN PGP PUBLIC KEY BLOCK----- and ending with -----END PGP PUBLIC KEY BLOCK-----.
Paste the GPG key to GitHub Settings as the figure goes below.
The Disqus comment system is loading ...
If the message does not appear, please check your Disqus configuration.